You can't hire 10,000 engineers.
Your SecOps team was lean before AI made attackers faster. They can't keep up with every endpoint signal or network event.
You lost the context.
Security evidence is everywhere, in every form, and evidence is not only logs and traces
You're too late to react.
AI lets attackers test more paths, adapt faster, and scale campaigns with less effort. Static rules and alert queues were built for a slower world
Querying is too slow.
The SIEM wasn’t built for today’s pace. It was designed for humans to query, not for AI to reason
100x your security engineers
Scale your best analysts’ judgment across every alert, hunt, and response workflow
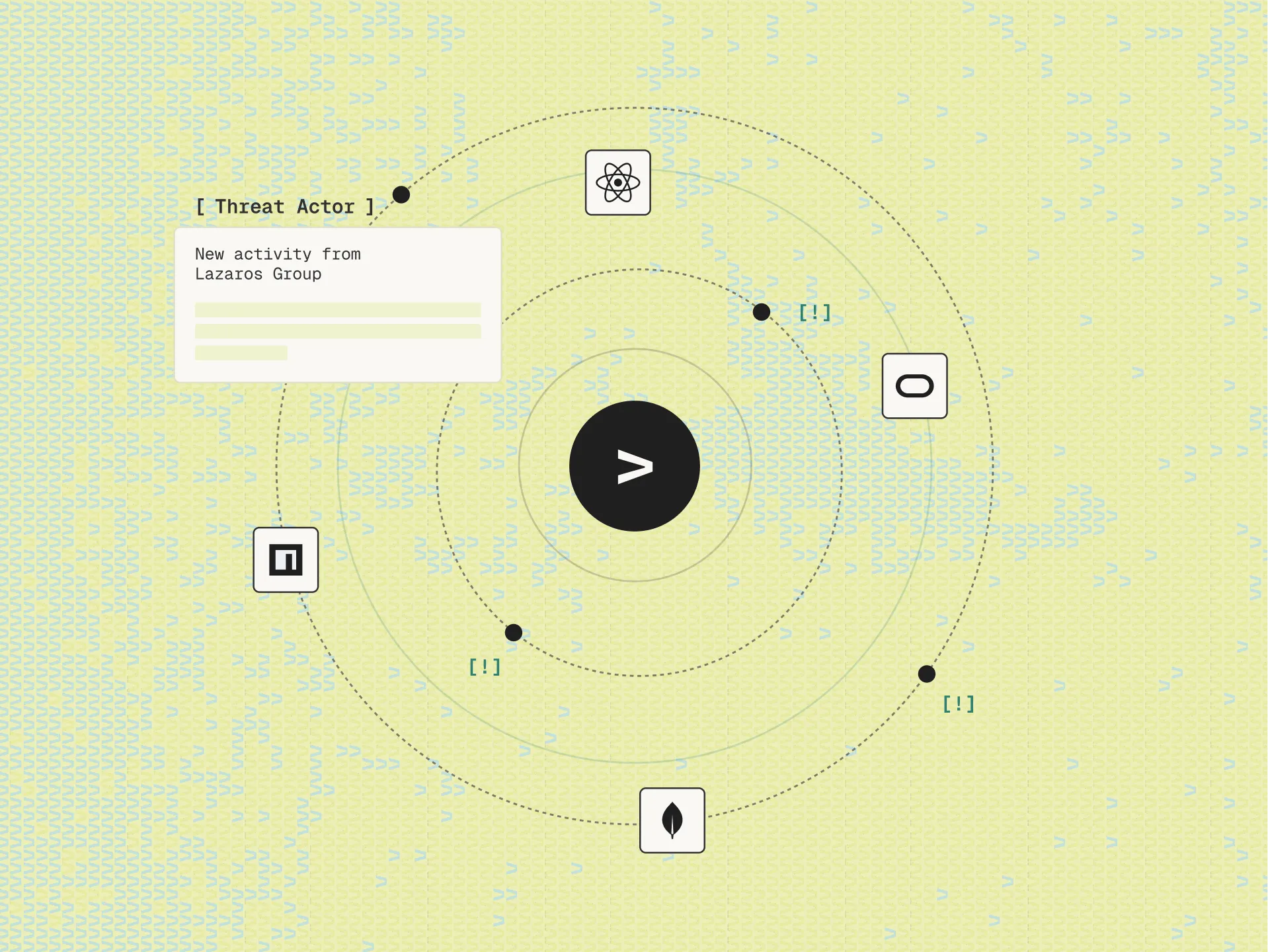
Never miss a trace
Continuously hunt and investigate across your existing stack, not just the data you centralized
Break the vendor lock
Reduce SIEM dependency, tool sprawl, and cost pressure while keeping your security operations flexible
No ingestion. No manual queries.
Complete SecOps platform.
Live Context Layer
Operate over your entire stack using natural language, no matter where your data lives, how it is structured, or whether it sits in cloud, SaaS, or on-prem systems

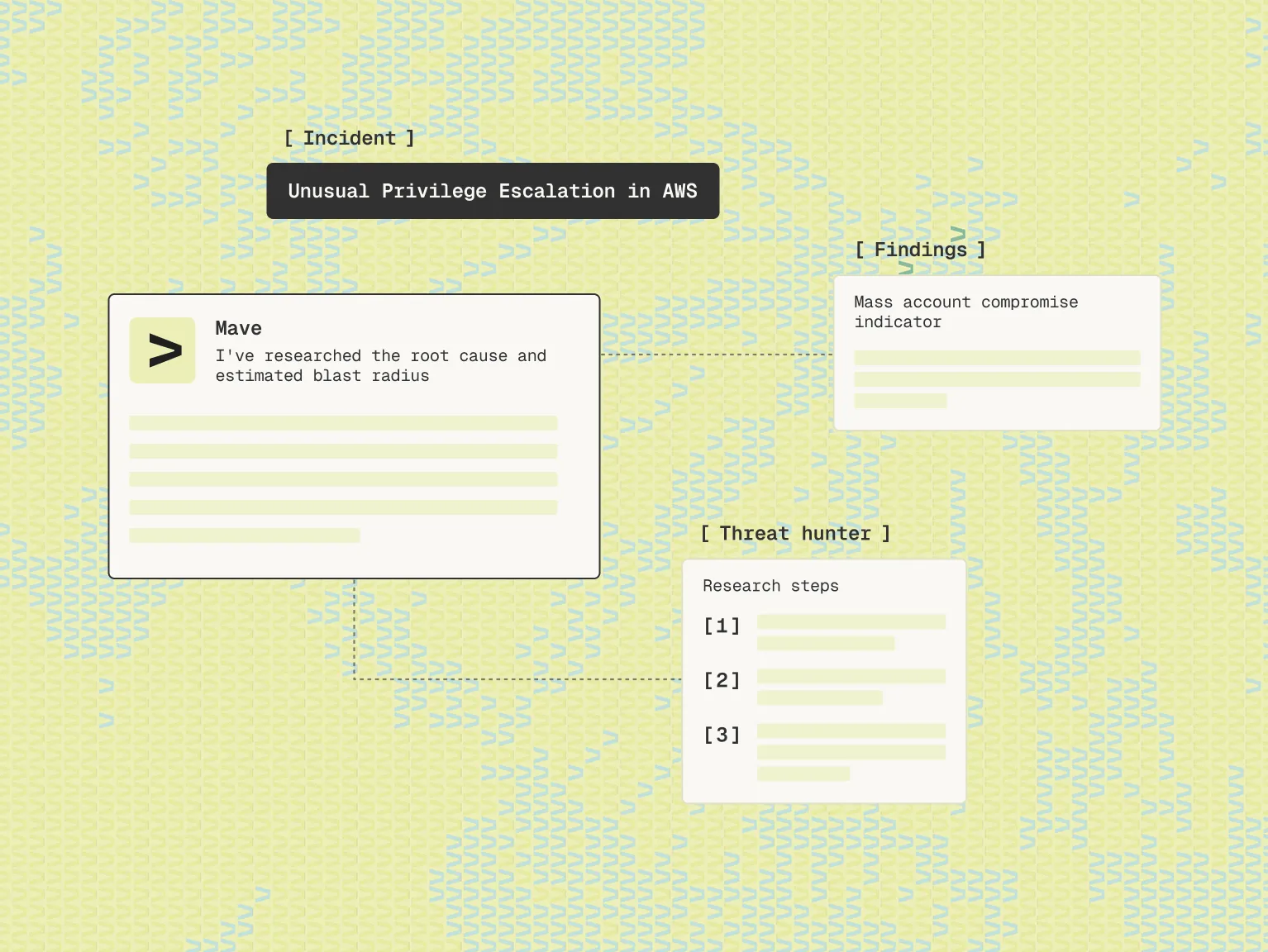
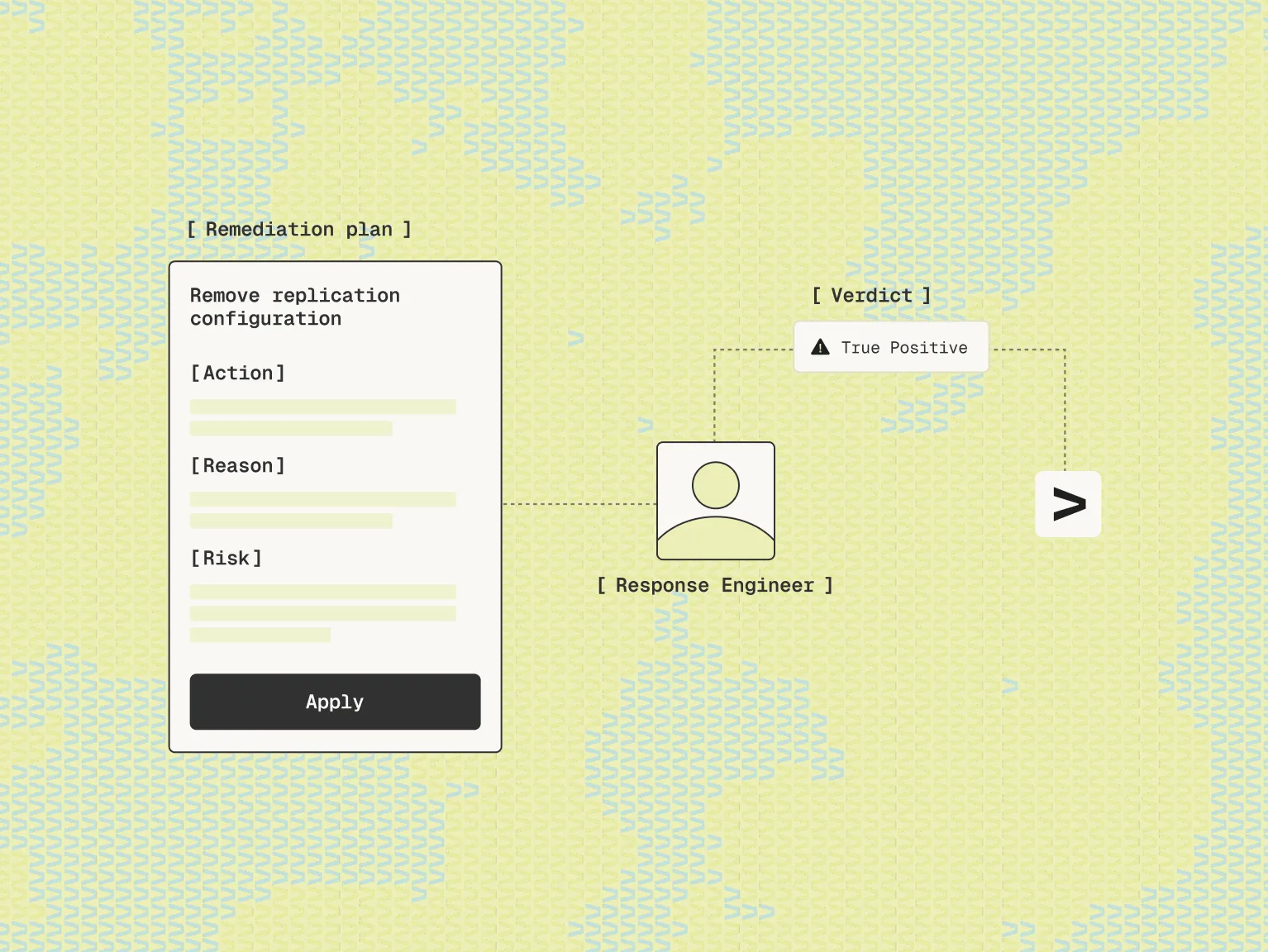
Agentic Workflows
Turn your engineers into conductors of security operations. Mave runs the repetitive work: detection, triage, hunting, and response, while your team guides and scales expert judgment

Connects in Minutes
Connect to your existing tools, workflows, and environments so Mave feels native from day one. Mave works with cloud and on-prem systems, existing ticketing flows, security tools, knowledge bases, and operational processes