SecOps requires a[new approach]
New Pace
Attackers iterate at machine speed. Threats adapt continuously, while SecOps workload keeps expanding.
New Fragmentation
Evidence lives across endless platforms: context breaks, correlation fails, response slows.
New Operating Model
SecOps can’t scale by tuning static rules or outsourcing to a black box. You need a governable layer that investigates, decides, and automates - across tools.
One platform to run detection and response across your stack
The Mave SecOps Operating System empowers security teams to detect, investigate, and respond across every system that holds ground truth - without a single-ingestion-point model.

Federated root-cause verdicts
Evidence-led triage across systems that produces a clear scope, timeline, blast radius, and defensible finding with an audit trail

Adaptive nation-grade coverage for the unknown
Continuous threat-hunting that evolves as your environment and adversaries change, so emerging tactics don’t become blind spots.

Closed-loop response and workflow automation
Contain, disable, revoke, quarantine - then document consistent and quick response across the stack.

SecOps that keeps up
Onboard in minutes
API-first, no ingestion required.
Connect scoped integrations via APIs and start pulling evidence immediately, without disrupting workflows or paying a data tax
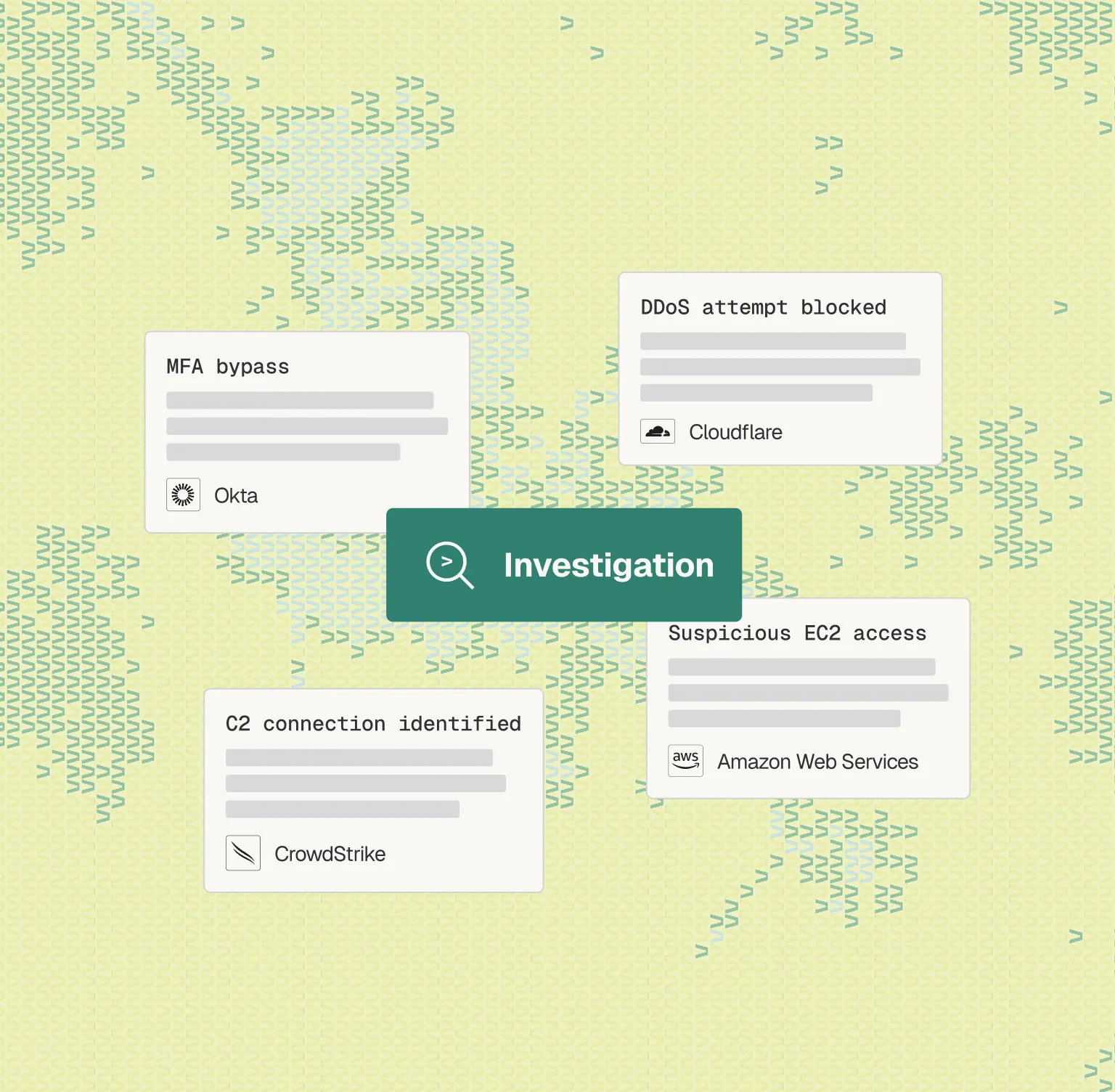
Federated correlation
One investigation across many systems.
Mave stitches identity, endpoint, email, cloud control plane, SaaS audit trails, data platforms, and IT workflows into a unified timeline, so context doesn’t break across tools, providing full evidence graph including supporting artifacts and rationale.
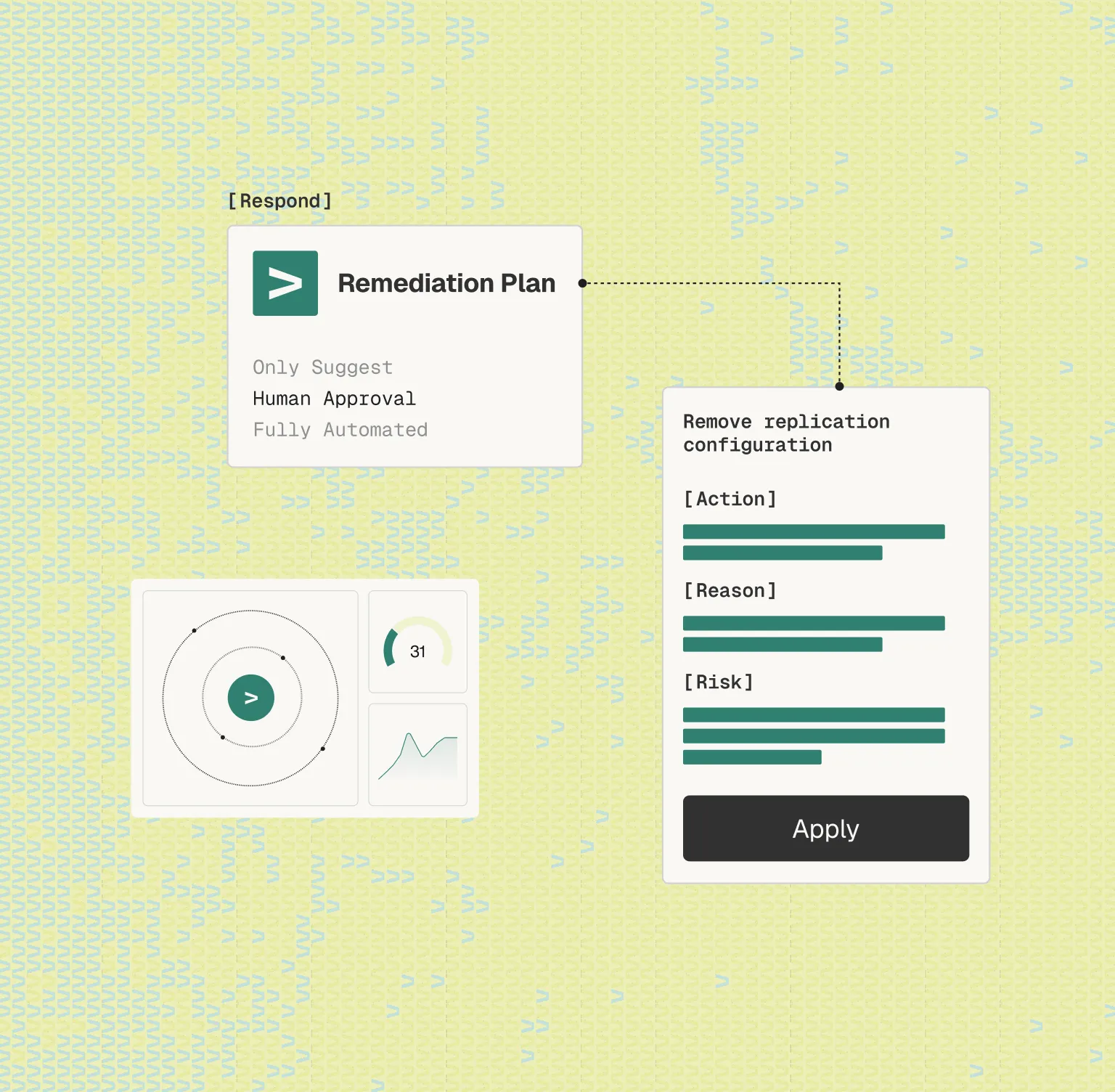
Risk Mitigation
Close the investigation loop.
Respond directly from Mave, with a clear view of incident blast radius
Consistent coverage hardening
Tuning that compounds.
When recurring noise is detected, Mave proposes detection improvements, validates impact, and routes changes through approval gates, so false positives will not reoccur.

Threat intelligence-driven coverage
Prioritize what matters to your environment and activate designated hunters to real campaigns and TTPs, with context and recommended next steps.

Single deep investigation interface
Ask Mave.
Ask natural language questions across connected systems and get unified, evidence-backed answers, without manual pivots or ad-hoc searching.

Cut costs & Remove Vendor Lock-In
Keep data where it lives.
Reduce reliance on “ingest everything”, keep systems of record as sources of truth, and evolve your stack without rebuilding your SecOps logic from scratch.
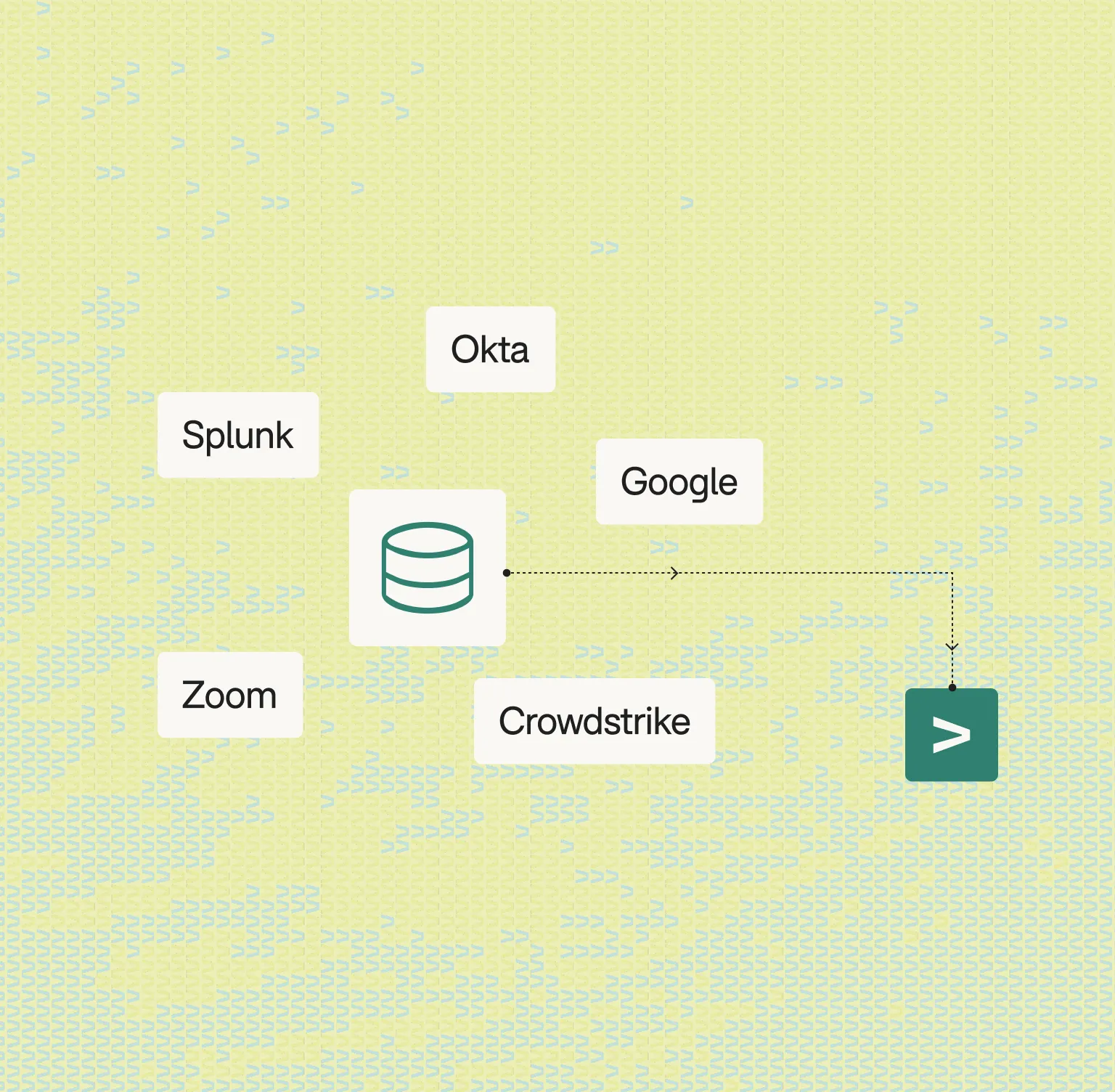
Yes, Mave works with your stack
Mave is platform-agnostic, integrating across the security and IT ecosystem to pull ground-truth evidence and route decisions back into your existing tools.













.webp)